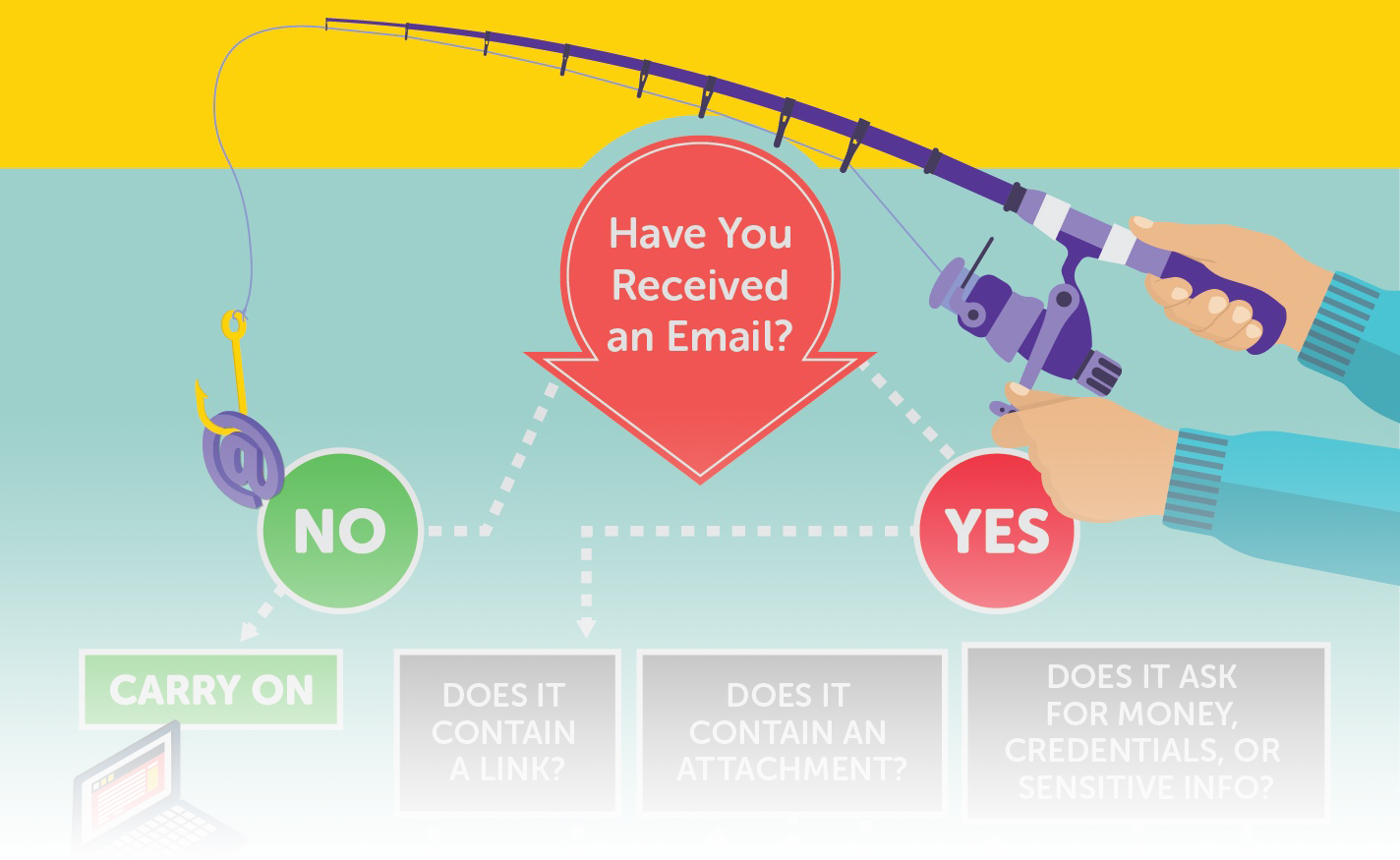
Avoiding Phishing Emails
Avoiding Dangerous Links
What Can Dangerous links from Phishing Emails Do?
- Confirm your identity to target you in the future.
- Trick you into entering credentials for a well known website on a fake website.
- Take control of your browser to download malicious code or ransomware.
URL Manipulation Warning Signs
- Shortened URLs: Attackers can shorten a malicious URL to hide its true destination, such as https://bit.ly/3i0Myc2. This gives the user less information about where they are being directed and thus makes them more susceptible to attacks.
- Number-based links: Attackers can use URLs that only consist of numbers, such as http://172.217.4.174, to hide malicious sites.
- URL Look-alikes: Attackers can use URLs that are close to real websites, such as “walrnart.com” rather than “walmart.com,” hoping that the user will not notice the difference between the malicious URL and the real URL.
- Hyphens: Attackers will use domain names that contain brand names but are hyphenated, such as https://ama-zon.com/. This often goes unnoticed by the user and leaves them vulnerable to an attack.
Before You Click on a Link
- Read the web address! If you don’t recognize the link, don’t open it.
- Only click on a link if you are expecting it, such as an order confirmation.
- Log in to your account from a URL you trust if the email requests action on an account, to see if action is needed.
- Hover over the link to preview it before clicking to examine the URL for suspicious characteristics.
- Use a search engine to verify that the domain shown is the correct domain for the website that the email is leading you to.
Avoiding Dangerous Attachments
How Can Email Attachments Be Dangerous?
By opening a suspicious attachment, you leave open the possibility of malware being installed on your computer without your knowledge. This malware can:
- Enable attackers to access, control, and record information stored on your device.
- Scan your device for email addresses and send the infected message to them.
- Spread quickly through your employer’s networks via your device, which enables attackers to quickly acquire and leak sensitive or confidential data.
File Name Extensions
- Avoid files that have extensions you are not familiar with, such as .exe, .msi, .dmg, .pkg, .mpkg, .js, .psc1, and .csh.
- Use caution with compressed files that have extensions such as .zip, .jar, .rar, .tar, and .7z.To bypass email filters, attackers will sometimes send compressed files with malicious contents.
- Do not enable macros that you did not define when viewing Microsoft Office documents.
What to Do When Receiving Email Attachments
- Check the Content of the email. Read the email before opening the attachment. Does the file extension match the type of content that you’re expecting given the context of the email?
- Contact the sender about the attachment, confirming that they sent the attachment and mean for you to open it. This can protect against email spoofing, where an attacker disguises an email address to make it look like one from a trusted source.
- Search for the topic of the email via a search engine. If the email is a scam, there could be an online discussion about it.
- Report the email to ITS if you have any doubt.
Data Entry Phishing
What Is Data Entry Phishing?
Data entry phishing is the process of luring users into entering sensitive information on fake websites. Users are typically targeted for information such as:
- Personally identifiable information (PII)
- Account log-in information
- Proprietary confidential information
- Bank account information
Data Entry Phishing Process
Data entry phishing happens in three steps:
- Attacker sends a phishing email, urgently asking the user to click on a malicious link.
- User clicks the link, which leads to a website that looks real.
- User enters their information, giving it to the attacker.
What Makes Data Entry Scams Dangerous?
- You can fall for them without realizing it. Often, once you have entered your information on the fake site, the fake site will redirect you to the real site that it was imitating. This makes it harder to realize that you have given away your personal information.
- Anti-malware programs often will not detect them since nothing is being installed on your computer.
- When attackers gain credentials for an organization’s systems, they can put the whole organization’s data at risk of being stolen.
How to Protect Yourself
- Be cautious of emails that ask you to click a link or enter your personal information or credentials. Credible businesses rarely ask for your personal information or ask you to click a link in an email to reactivate an account.
- Pay attention to the link and look for signs of the website being a phishing website. These signs include:
- The URL does not start with “https.” A URL starting with “https” means that the data going between the website and your computer is encrypted and secure. While attackers can use “https,” a website asking for sensitive information without using https is immediately suspicious.
- The URL is not accurate for the company or service you are attempting to access. For example, the website’s URL may be “wolmart.com” or “wal-mart.com” rather than “walmart.com.”
- The website contains errors. Telltale signs of phishing websites include poor grammar or threatening language, blurry logos or images, and layout/styling errors.
- Ask for help if a site or email looks like it could be malicious. You can ask a colleague or submit a ticket to ITS if you feel that you may be at risk.
If You Have Revealed Sensitive Information About the University
- Immediately report the incident to ITS.
- If you have provided banking information, contact your financial institution.
- Change any passwords you may have revealed.
- Monitor the affected account for any signs of identity theft.
More Resources
Report Phishing to Google
If You Are Using the UC Santa Cruz Gmail Web Interface:
- Open the message in Gmail (in your web browser).
- Click the three vertical dots (⋮) next to reply.
- Choose "Report phishing".
For more Gmail information, visit the following pages:
Test Your Phishing Know-How
- Google Phishing Quiz: Google has published a fun, informative quiz to test if you can spot when you're being phished.
- Open DNS Phishing Quiz: Open DNS has published an effective quiz to help you differentiate between phishing websites and legitimate websites.
The Phish Bowl
For examples of email phishing scams that are being sent to UCSC staff, faculty, and students see The Phish Bowl.

