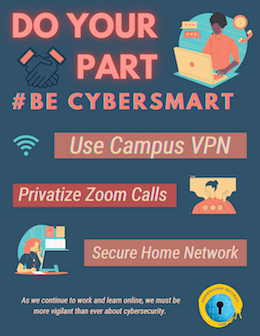
While working, learning and teaching remotely, we all need to be hyper-vigilant about good cyber hygiene practices. Do Your Part, #Be Cyber Smart by being aware of the tools that ITS services offers students, staff and faculty to keep their devices secure. Also, inform yourself about how to keep your home network and frequently used software secure.
So, what are some critical steps that we can take to protect our online safety and security?
Use Campus VPN
Use the Campus Virtual Network (VPN). Campus VPN is a free service that enables a secure connection to the UCSC network from off campus. The VPN will encrypt your data against potential intruders. Set up all of your computers and mobile devices to use Campus VPN and connect when you are located off campus, by following this quick start guide. The Campus VPN is required for any work involving P3-P4 data. University data is classified into one of four categories, known as Protection Levels.
Benefits to using Campus VPN
- Network Traffic Encryption
- When you connect to another site using a VPN, your traffic is encrypted from your computer through the network to the VPN hardware at UCSC.
- This is so that if anyone intercepts the traffic, they cannot see what you are doing unless they can break the encryption
- Access UCSC Resources
- When you are using a VPN connection, regardless of where you are, it will appear to the internet that you are on campus. You will have a UCSC IP address instead of the one you have at home or while traveling.
- This allows you to connect to resources that you would not otherwise be able to connect to remotely.
Keep Zoom Private
Zoom video conferencing software has become such an essential part of our lives in the past year. Although Zoom may be used mainly for academic and professional purposes, intruders or “zoom-bombers” can cause issues. We’ve all witnessed or heard of these instances that not only disrupt the learning and working environment but also cause meeting participants to feel vulnerable and unsafe online.
Zoom is configured by default to help reduce the possibility of unknown or unwelcome guests joining a meeting or webinar like masking phone numbers and encrypting every session. In September, Zoom made a global change to Zoom accounts that requires all meetings to have a Passcode or a Waiting Room enabled. More information on making your Zoom sessions private.
Secure Your Home Network
Another essential step in keeping your data and network secure is to secure your home network. When working remotely, employees are responsible for keeping documents, sensitive data and other work-related materials confidential and secure. You can secure your home wireless network by following these effective steps:
- Change the default admin password
- Enable WPA2 encryption
- Use a strong password for your wireless network
If you are using an unsecured network (public wifi) you should be connected to the Campus VPN. As the majority of us are now working and learning remotely, there is no guarantee that the network we are using is safe. Read this article from SANS Security Awareness Institute, to see what other ways you can protect your home network from intruders. Taking some simple steps can go a long way to creating a cyber secure home.
UC Approved Tools
In order to remain safe while instructing or learning, please make sure you’re using tools approved by the university. If instructors fail to check on the security standards of the tools they’re using, students can still check that it is approved by the university and safe to use. Read through this page to learn which tools are recommended and supported by the university for remote learning.
In addition to using UC approved applications and tools, take caution when choosing a third party app whose supplier we do not have a contract with. Guidance on Use of Third Party and Cloud Services.
For more information on how you can make secure choices, visit https://its.ucsc.edu/security/stay-secure.html.