ON THIS PAGE:
This October we are celebrating the 20th Annual Cybersecurity Awareness Month. This began in 2004 when the President of the United States and Congress declared the month of October to be Cybersecurity Awareness Month.
Here at UCSC, we celebrate UC Cybersecurity Awareness Month (UCCAM) to remind everyone of the importance of protecting our digital selves and our data. This year the Information Security team has partnered with the Privacy Office and the Office of Retention to highlight 5 topics that emphasize ways to be more cybersecure. We have also created a variety of ways that you can participate.
Strengthen Your Login Game
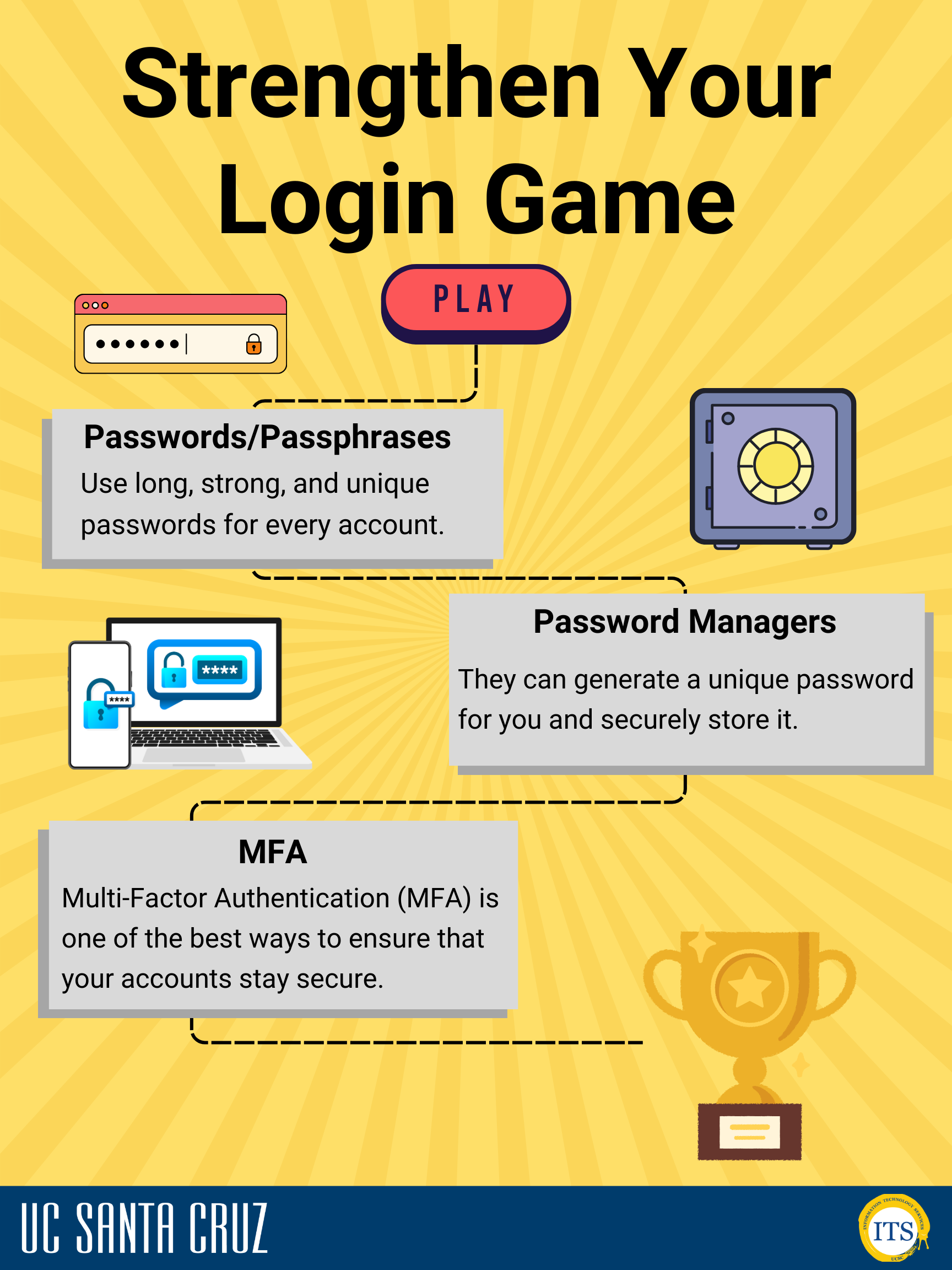 Passwords/Passphrases: Use long, strong, and unique passwords for every account.
Passwords/Passphrases: Use long, strong, and unique passwords for every account.
- Ex. PurpleBurgerBears is stronger than Poodle3$.
- Password Managers: They can generate a unique password for you and securely store it.
- Multi-factor Authentication (MFA): MFA is one of the best ways to ensure that your accounts stay secure. Read more about MFA for your UCSC accounts
- Learn more about password security
3rd Party Apps
Procurement & Contracts
-
 Using a campus procard does not imply the services are covered by UCSC or UC-wide agreement.
Using a campus procard does not imply the services are covered by UCSC or UC-wide agreement.- If you want to use an app for P3-P4 UC institutional data, you must submit a requisition.
Curious about AI?
- UC Develops Principles to Guide Use of AI
- Recommendations to Guide the University of California’s Artificial Intelligence Strategy
Check out approved services (Software for Faculty/Staff and Student Software Services)
and more general guidance.

Data Privacy
Privacy consists of the individual's ability to conduct activities without concern of or actual observation and the appropriate protection, use, and release of information about individuals.
Some Key Data Privacy Concepts:
- Collection of personal information shall be limited to that which is necessary for lawful purposes directly related to a function or activity of the collector.
- Notice: Collection documents must include notice identifying the purpose for which information is collected and used.
- Accuracy: Reasonable steps shall be taken by the collector to ensure the information is accurate, complete, up-to-date, and relevant to the purpose for which information is collected.
- Use: Personal information shall not be used or disclosed other than for purposes collected, except with consent of the individual or when required by law.
- Access: Except under express provisions of the law, an individual shall be permitted to inspect all personal information in any record containing personal information that is maintained by reference to that individual.
- Amendment: An individual has a right to request in writing an amendment of a record.
Some Key Data Privacy Best Practices:
- Apply privacy principles to everyday work.
- Determine whether information is necessary and relevant to document/process.
- Adopt "clean desk" practices: secure documents in locked cabinets; lock computer when unattended.
- P3 and P4 information should not be included in email. What to do if P3 or P4 information ends up in email.
- Ensure data is encrypted if electronic systems are unsecure and do not use unsecure email to transmit.
Learn more at privacy.ucsc.edu.
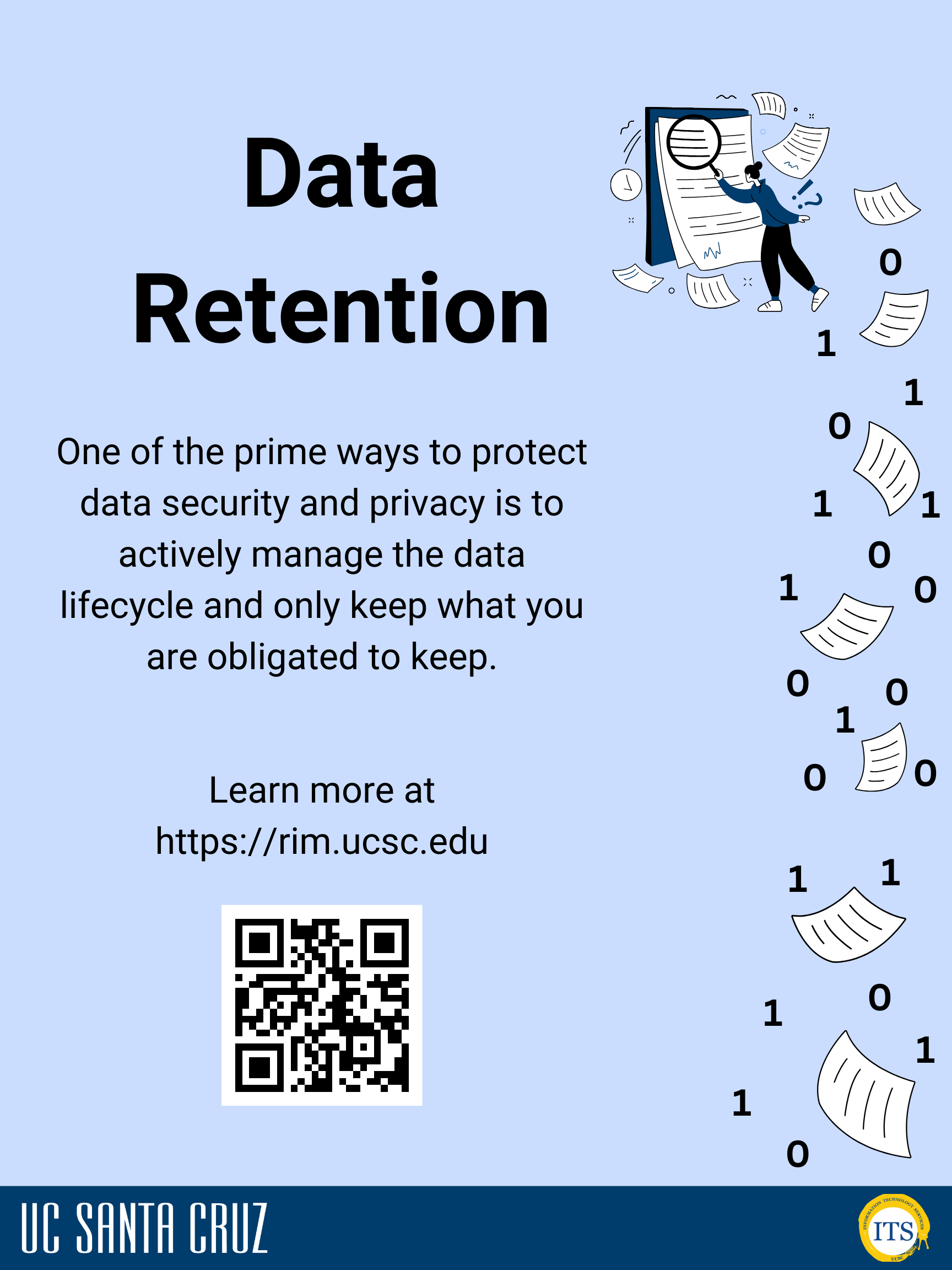
Data Retention
One of the prime ways to protect data security and privacy is to actively manage the data lifecycle and only keep what you are obligated to keep.
The key concepts of data retention at UC are:
- Each type of content has a different retention timeline driven by State and Federal laws, and third-party obligations. Units store data of numerous content types based on its function and activity.
- The UC Records Retention Schedule is the principle guiding document and the agreement between all 10 campuses on how long to store data.
- A unit is only “Office of Record” for data that the unit produces and maintains as a part of its business function. For example, Financial Affairs is the Office of Record for travel reimbursements and your unit’s copy can be purged as soon as it is no longer being referenced.
- A "record" requires content and context. Raw individual data points in individual tables do not constitute a "record." Once data is assembled or queried into a report or document, that document is a record that must be classified according to the type of content.
- Protection classification does not equate to any legal retention requirements.
- Unmanaged data, for example, old forgotten data that your department has been storing but doesn’t really know what to do with, present both legal and reputational cost to the university.
For more guidance on managing the data lifecycle, see https://rim.ucsc.edu.

Report It!
Reporting Phishing
DO REPORT an email phishing attempt immediately to Google
If you are using the UCSC Gmail web interface:
- Open the message in Gmail (in your web browser)
- Click the three vertical dots ' ⋮ ' next to reply
- Choose 'Report phishing'
Learn more about phishing
Reporting a Security Incident
You can report any incident! Whether it be a stolen device, compromised system, policy, and privacy violations, etc.
To report a security incident to ITS:
- Go to its.ucsc.edu/security/index.html
- Click "Report an Incident”
- You will be redirected to a form for you to fill out
Webinars
Protecting Your Online Identity in the Age of Big Data and AI (Oct. 5 at 11 a.m.)
UC Cybersecurity Awareness Month Webinar (Oct. 9 at 11 a.m.)
A Tale of Two Industroyers (Oct. 19 at Noon)
Find even more webinars available to all UCs for Cyber Security Awareness Month 2023.
Learn more about our UC Cybersecurity Awareness Month campaign
Check out our official UC Cybersecurity Awareness Month webpage to…
- Learn more about how you can be more cybersecure
- Participate in activities and games
- Enter raffles to win prizes!
Get Help
- If you need assistance, contact the ITS Support Center
- To report a security incident, visit UCSC’s Report a Security Incident page